What is Trojan:Win64/Zebracon.A!dha?
Trojan:Win64/Zebracon.A!dha is an ultimate threat to any Windows computer as it is a violent member of the Trojan virus community. This perilous threat is a notorious form of spyware designed to expose the security of victimized machines and allow remote access to the machine to hackers. This cunning malware infection can easily intrude on your Windows computer without your knowledge. It can hide deep into your system and execute several malicious processes that will abruptly affect your system’s speed and performance.

Trojan:Win64/Zebracon.A!dha can stay undetected on your system for a long time by changing its name and disguising its appearance. It can create multiple copies and spread them at various locations on your system with different names to avoid its complete removal at once. This nasty virus is a major threat to your system as it is hard to detect and remove using any regular anti-virus because it disables all your security-related programs upon intrusion.
How does it infect your PC?
Trojan:Win64/Zebracon.A!dha virus mostly spread through bundled freeware programs, cracked software, illegal patches, etc. that users normally download from low-quality websites. Hackers can also send this threat as spam email attachments pretending to be important emails sent from any company or legitimate service. Your system could also get infected by similar threats when you visit porn torrent websites, share files on unsafe networks, click on misleading ads that redirect your browser, and various other social engineering methods.
One thing you need to understand is the Internet is full of threats like this which can easily enter your machine if you are not careful enough. So you must scan all email attachments before opening, do not open suspicious emails from unknown senders, do not download cracked programs or software, always choose a custom installation method, and read EULA and Terms of Use before installing any free application to avoid Trojan:Win64/Zebracon.A!dha virus or any other malware intrusion.
Why it is dangerous to your PC?
Invading your system is just the start and Trojan:Win64/Zebracon.A!dha has big plans to destroy your computer. It not only damages your system performance but also corrupts your files, steals your personal information, and brings other threats to your system. This nasty threat is designed to intrude into your system so that hackers can easily access all the information stored on your computer and can drop other threats as they need or desire to make the most profit. It can show unwanted ads, pop-ups, warning alerts, messages, offers, and other kinds of elusive and deceptive advertisements on your machine.
This virus can redirect your browser to malicious websites to bring more threats and download additional updates for itself. It can modify your DNS settings to control your Internet settings and connect to a remote server secretly to render secret information directly to hackers. This deceptive Trojan malware can record your keystrokes and your online activities to gather sensitive information like social media login details, credit card information, IP address, etc., and share with creators for use in illegal activities and earn profit. It can open a backdoor on your system to allow remote access to your system through which hackers can easily gain access to all your system files and information.
How to Remove Trojan:Win64/Zebracon.A!dha
Removing this dubious Trojan virus manually will take lots of time and even a little mistake can break your PC instantly. Regular Anti-virus applications fail to completely delete this infection, so we advise using SpyHunter 5 Anti-Malware.
It is a powerful Anti-Malware capable of removing threats like Trojans, Malware, Ransomware, Spyware, Browser Hijacker, Adware, Redirect Viruses, PUPs, Worms, Rootkits, etc. SpyHunter’s Advanced System guard will also block threats from intruding on your computer in the future.
How SpyHunter 5 Anti-Malware Works
- You will begin by downloading the software on your system for which you have to click on the below download button.
Geek’s Recommendation
Threats like Trojan:Win64/Zebracon.A!dha keeps getting back on the machine if all associated files are not removed. So you are advised to use a powerful Malware Removal Tool to run a thorough scan of your PC and delete all threats at once.
SpyHunter 5 Anti-Malware offers a 7-day fully-functional Free Trial. Credit card required, NO charge upfront. No charge if you cancel up to two business days before the trial period ends. Read SpyHunter 5 Review and Free SpyHunter Remover details.
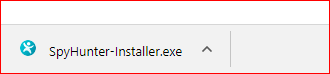
- Once the software has been downloaded, double-click on SpyHunter-Installer.exe to install the Anti-Malware program on your PC and proceed with the setup.
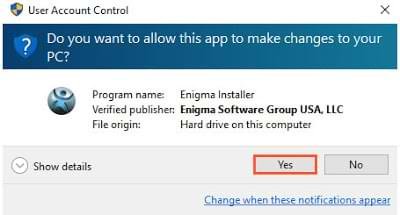
- After installation, you will need to launch the Anti-Malware application. From the welcome screen click on the Start Scan Now button to initiate a new scan of your PC.

- Once the scanning process begins, it will take some time to run a thorough diagnostic of your PC and find all hidden threats and malware.
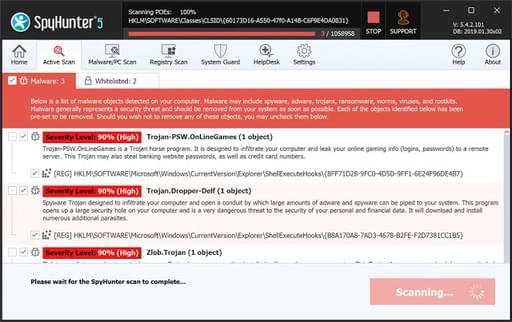
- Soon you will find a complete list of all the threats on your system screen. Then you will need to click on the Next button to delete all the viruses.

Leave a Comment