Exploit:JS/OVCExploit.gen is a dangerous Trojan malware infection created by cybercriminals with the motive of making money online through illegal and fraudulent methods. This dubious infection is a sneaky piece of threat that is able to attack all versions of Windows PC. However, older versions like XP/Vista and Windows 7 are more vulnerable to this infection because of stopped security support. It is very important to keep your Operating system and other programs up to date to avoid any malicious threat like Exploit:JS/OVCExploit.gen. Keep in mind that only download updates from official sites and avoid pirated software to keep your computer safe.
Threats like Exploit:JS/OVCExploit.gen keep getting back on PC if all associated files are not removed. So you are advised to use a powerful Malware Removal Tool to run a thorough scan of your PC and delete all threats at once.
Special Offer SpyHunter 5 Anti-Malware offers a 7-day fully-functional Free Trial. Credit card required, NO charge upfront. No charge if you cancel up to two business days before the trial period ends. Read SpyHunter 5 Review, and Free SpyHunter Remover details.What is Exploit:JS/OVCExploit.gen
Exploit:JS/OVCExploit.gen is a kind of computer menace that secretly intrudes on the targeted machine and enjoys controlling the compromised system remotely. It is a violent Trojan malware that is ready to intrude on any Windows computer and keep hidden for an extended time while not being detected. It can change its name to disguise its presence on your PC which is why most of the security programs fail to detect it soon enough before it causes any severe problem.
Users don’t usually find out about Exploit:JS/OVCExploit.gen virus until it starts doing its evil work. It is very important that if you suspect the presence of this infection on your machine, you must check your system thoroughly and remove it properly to avoid any serious altercations in the future.

Threats like Exploit:JS/OVCExploit.gen virus can be very dangerous not only to the infected system but to the user as well. In today’s modern era, everybody likes to store their private and sensitive information on their PC for safekeeping and simple access. If anyhow your computer gets hacked or attacked by a nasty Trojan malware that can destroy your important files and transmit your personal information to hackers.
Exploit:JS/OVCExploit.gen virus is programmed to collect personal details of the user like social media login passwords, credit card number, IP address, etc. by tracking browsing history and recording keystrokes. It is a very significant threat because it carries out a very sophisticated attack on the victimized machine from multiple sides. This nasty Exploit:JS/OVCExploit.gen virus will start a series of malicious activities that will completely destroy your computing experience. The working of each explicit Trojan virus is completely different and fully depends on why it was created, however, they all have some quite common qualities.
Issues caused by a typical Trojan virus
- Sneak into the targeted computer without users’ permission.
- Redirect your browser to malicious sites and show annoying pop-ups.
- Steal your passwords and use a keylogger to record your keystrokes.
- Collect your personal and sensitive information and share it with hackers.
- Disable your antivirus in addition to the firewall to make the system more vulnerable.
- It can Install other threats and malware on your system secretly.
- Show fake tech support pop-up that can lure you into a scam.
- It can allow hackers to remotely access your system without permission.
Exploit:JS/OVCExploit.gen: Threat Analysis
| Name | Exploit:JS/OVCExploit.gen |
| Type | Trojan |
| Threat Level | High (source to distribute other harmful threats). |
| Symptoms | Slow PC, unresponsive programs, unexpected errors, fake pop-ups, browser redirection. |
| Distribution | It could be distributed through spam emails, bundled freeware, porn, or torrent sites. |
| Damage | Steal personal data, corrupt files, bring other threats, and give remote access to hackers. |
| Removal | Download SpyHunter 5 Anti-Malware |
Exploit:JS/OVCExploit.gen intrude your PC silently
Exploit:JS/OVCExploit.gen virus can get into your system through various different tricks. Hackers use lots of different methods to hook for new victims. Your PC can get this malware as an attachment to spam emails, sent by hackers with fake names. These emails may look genuine such as credit card bills, phone bills, bank statements, and so on. Most of the users fall for this and don’t check the sender’s email address or other information. Opening such emails, downloading attachments, and opening them without scanning can infect your PC.
This noxious Trojan malware is also being spread bundled with free third-party programs, shareware, cracked software, illegal patches, and fake updates. Apart from this, Exploit:JS/OVCExploit.gen virus can also infect your machine when you visit malicious websites, porn, or torrent sites, click on misleading ads or share files on unsafe websites. You can see this virus can easily sneak into your machine using any of these tricks and you won’t even notice until it starts creating problems.
Removal tips for Exploit:JS/OVCExploit.gen virus
Finding Exploit:JS/OVCExploit.gen virus manually could be a hectic job no matter how trained you are because it keeps changing its location and file name. It can also spread its copies at a different location with different names. This notorious threat could also create new registry files to get back on your machine in case if it gets deleted anyhow.
For the permanent removal of this Exploit:JS/OVCExploit.gen virus you must remove all its associated files. It not only endangers your system security but also puts your privacy at risk. So it is better if you remove this infection from your system as soon as you find out its presence. We have created a very detailed and step-by-step informative guide to help your Remove Exploit:JS/OVCExploit.gen virus completely and safely from your system.
Automatic Exploit:JS/OVCExploit.gen Removal Guide
As you already know that, Exploit:JS/OVCExploit.gen is a notorious and cunning malware that is not hard to remove easily by any user through manual means. This virus can keep coming back on the infected computer through files and shortcuts or settings that it has already created on your machine. Removing all those at once is the only way to get rid of this infection and stop it from getting on your system ever again.
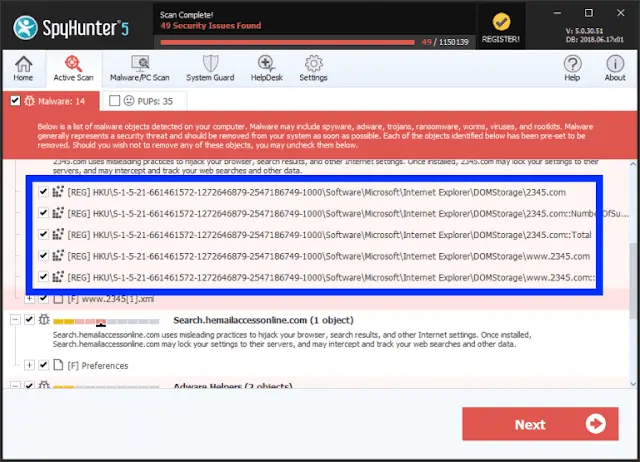
So the best way to remove Exploit:JS/OVCExploit.gen effectively is to use a powerful Automatic Removal Tool and save your time and efforts. This software is a well-trusted and very powerful anti-malware program that can detect all hidden threats like Trojan, Ransomware, Worms, Spyware, Rootkits, and many others. It also provides 24X7 customer support and one-on-one Spyware HelpDesk support for Custom Malware removal. Advanced System Guard feature detects and removes threats in real-time. It has a very User-Friendly Interface and regular Malware updates make it most effective against the latest malware attacks.
How SpyHunter 5 Anti-Malware Works
- First, you need to click on the below download button to get the software.
Geek’s Recommendation
Some time threats like Exploit:JS/OVCExploit.gen keep getting back on the machine if all associated files are not removed. So you are advised to use a powerful Malware Removal Tool to run a thorough scan of your PC and delete all threats at once.Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)
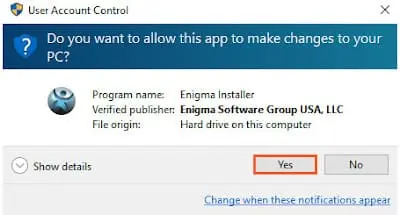
- Then double-click on the installer you downloaded to install the program.
- Launch Anti-Malware application and Start Scan Now of your PC.
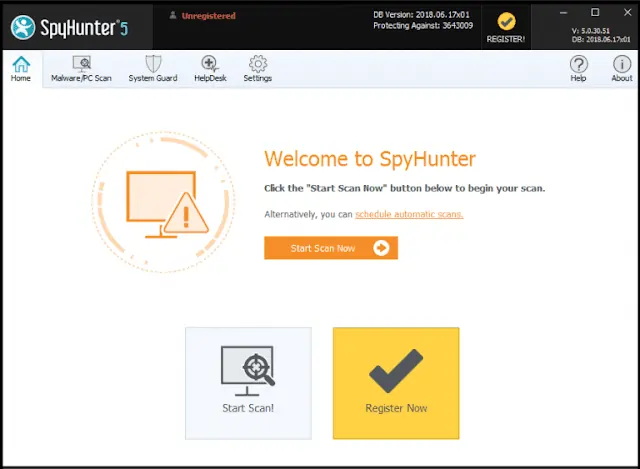
- Software will scan your PC for all hidden threats and viruses on your system.
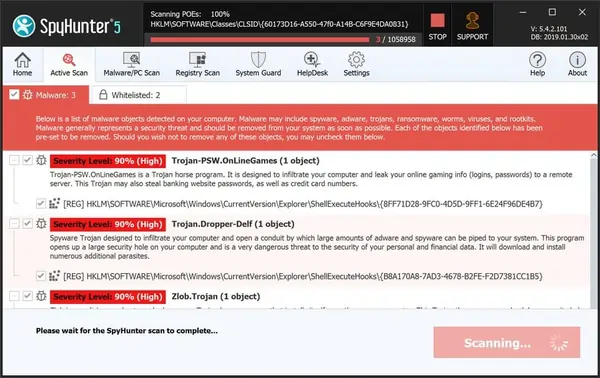
- Click on Next button to see results and delete Exploit:JS/OVCExploit.gen and other threats.
Manual Exploit:JS/OVCExploit.gen Removal Guide
- You have done this before, which means you have experience in removing the virus manually;
- That you know your way around PC and all necessary process and applications;
- You know about Registry entry and the Serious repercussions of any mistake;
- Make sure you can reverse any mistake made during Exploit:JS/OVCExploit.gen manual removal.
If you don’t attain any of the above standards, then manual removal could be a very risky idea. It is most likely best for you to use the Automatic Malware Removal Tool to find and delete Exploit:JS/OVCExploit.gen, which is totally secure and efficient method.
Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)
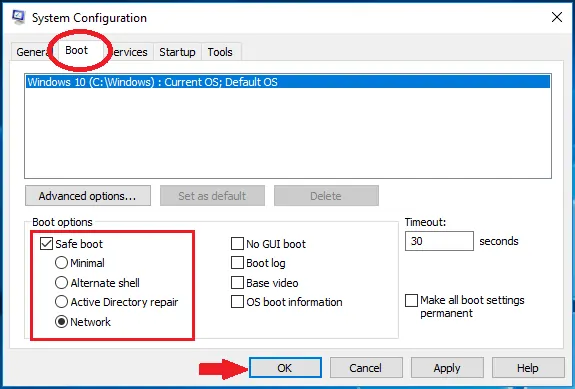
Start PC in safe mode with networking
- Press Windows Key + R buttons together on the keyboard.
- Type msconfig in the Run Box then click OK button.
- Click on Boot tab then System configuration window will appear.
- Choose Safe Boot, check network box, Click Apply, and press OK button.
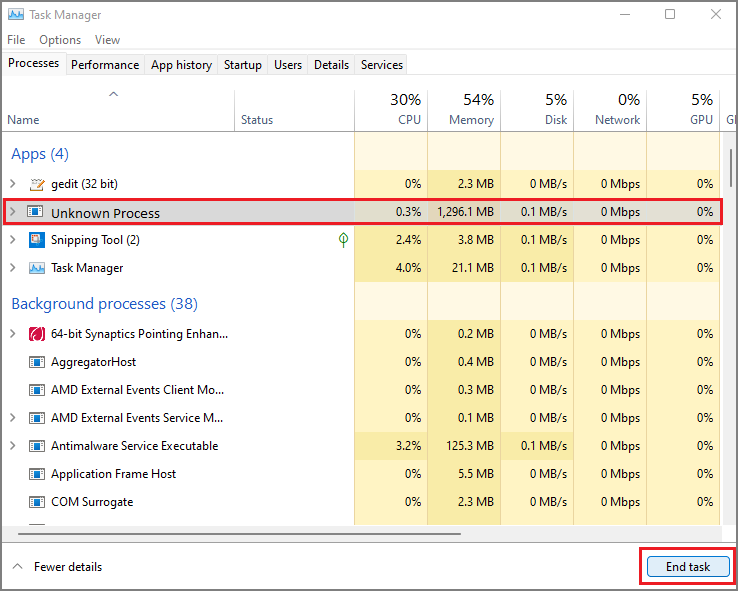
Kill Malicious Process From Task Manager
- Press Windows Key + R buttons together on the keyboard.
- Type taskmgr in Run Box and then click OK button.
- Find Exploit:JS/OVCExploit.gen related or any malicious process.
- Now right-click on it then click End process.
How To Uninstall Exploit:JS/OVCExploit.gen from Windows PC
- First of all Press Windows Key + R buttons together.
- Type appwiz.cpl in the Run Box and then click OK button.
- Now Programs and Features windows will appear on the screen.
- Find and remove all Exploit:JS/OVCExploit.gen related or malicious programs.
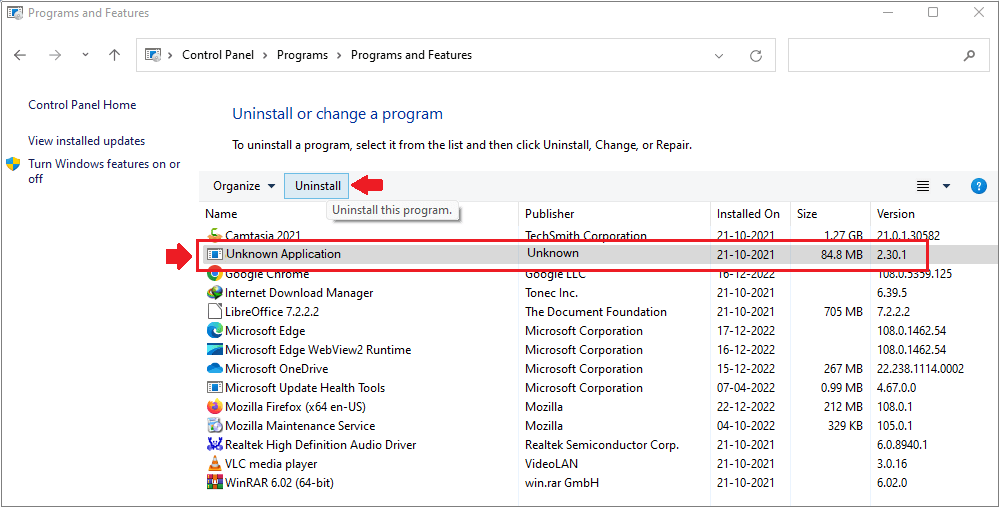
Remove Virus related Windows Registry entries
- Press Windows Key + R buttons together on the keyboard.
- Type taskmgr in Run Box and then click OK button.
- Registry Editor will open, then press CTRL +F buttons together.
- Now type Exploit:JS/OVCExploit.gen and then click on Find Next button.
- Find all the related entries and delete them one by one
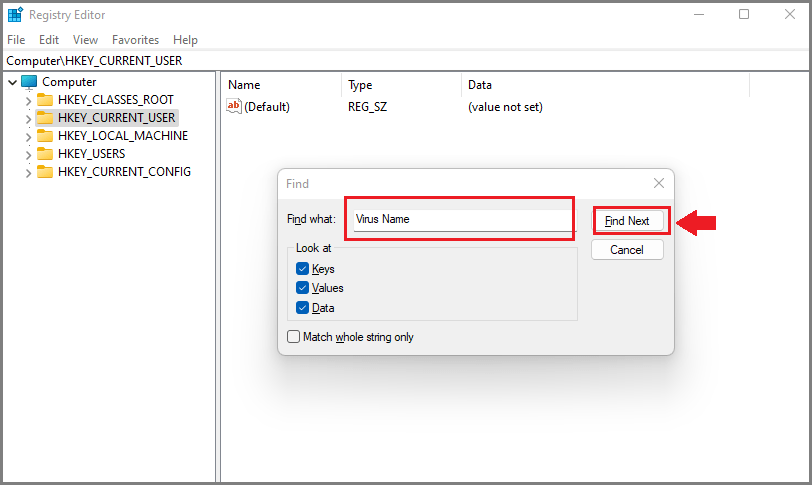
Warning: Meddling with Windows Registry files might not be a good idea if you don’t have advanced knowledge about registry files. Deleting the wrong file can break down your entire system. Proceed at your own risk, or just skip this step. You can choose the Automatic Removal method and avoid all the problems.
Remove Exploit:JS/OVCExploit.gen From MacOS
Stop Malicious Program From Activity Monitor
- First, you need to open Utilities folder on your Mac system.
- Find the Activity Monitor icon and double-click on it to open it.
- Find Exploit:JS/OVCExploit.gen related process, click cross button from upper left side corner to end task.
- A pop-up dialogue box will appear on the screen, click on Force Quit button.
Remove Exploit:JS/OVCExploit.gen From Application Folder
- First, go to Dock option (bottom of your screen) then click on Finder App.
- Now you have to open the Applications Folders to see all the programs.
- Find Exploit:JS/OVCExploit.gen or any other unwanted program then move it to Trash.
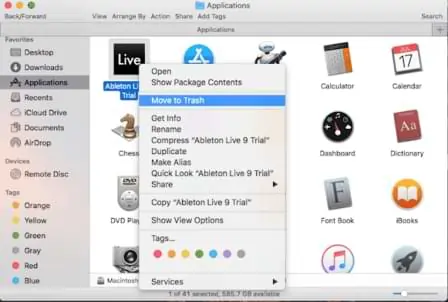
Attention: If you are using a Mac computer, then it could be quite difficult to remove Exploit:JS/OVCExploit.gen from your mac. The best way is to download ComboCleaner Mac Anti-Malware and see if it can detect all hidden threats and viruses on your computer. It’s really super easy and you should give it a try.
ComboCleaner Mac Antivirus allows you to scan your Mac for threats and viruses for free, but you will need to purchase a full license to remove found threats. Read EULA.Remove Exploit:JS/OVCExploit.gen From Browser
Most of the time, threats like this make several changes to the browser which helps it to track victims’ online activities. It is important to completely remove Exploit:JS/OVCExploit.gen from the browser or it may come back. Follow below steps to remove this infection from your browser.
Delete Malicious Extensions From Browser
Many spyware now has browser hijacking capabilities to show ads, offers, alerts, notifications, or stealing the personal information of the victim. Follow below steps to remove malicious extensions from your browser.
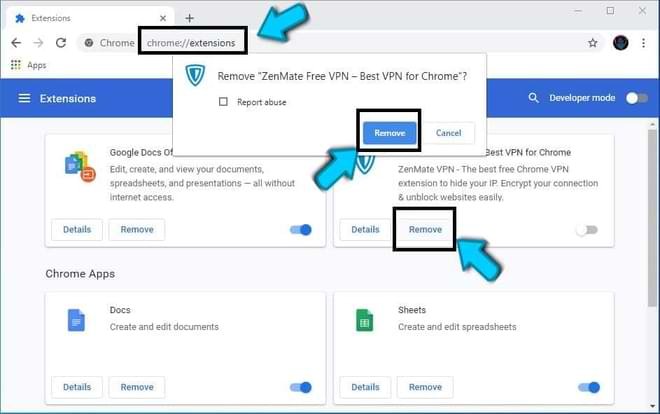
Remove Exploit:JS/OVCExploit.gen From Google Chrome
Note : Type or copy-paste – chrome://extensions in the URL bar of Google Chrome then press ENTER button to open the extensions page directly or follow below steps.
- Open Google Chrome browser, click the Menu (⋮) option from the upper right corner.
- Select More tools then click on Extensions option to find all installed Extensions on chrome.
- Choose Exploit:JS/OVCExploit.gen related extensions then click the trash can icon to remove completely.
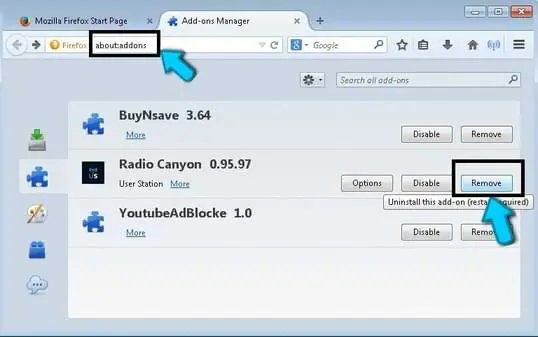
Remove Exploit:JS/OVCExploit.gen From Mozilla Firefox
Note: Type or copy-paste – about:addons in URL bar Firefox then hit ENTER button to open the extensions page directly or follow below steps.
- Open Mozilla Firefox browser, click on Menu (☰) option from the upper right corner.
- Select Add-ons option from the drop-down menu of the list.
- Choose the Extensions option to see all installed extensions on your browser.
- Choose Exploit:JS/OVCExploit.gen related extensions then click on Remove button.
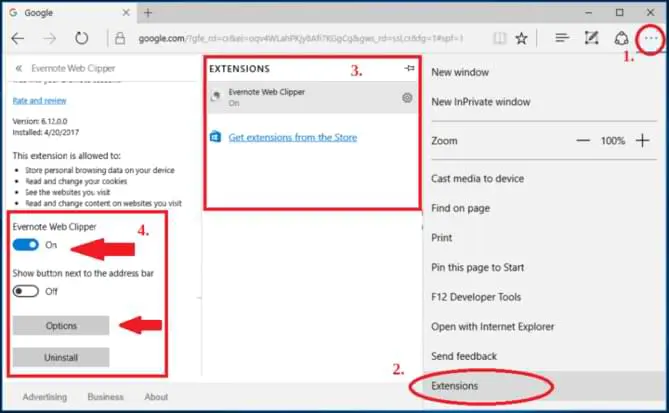
Remove Exploit:JS/OVCExploit.gen From Microsoft Edge
- Open MS Edge browser, click on More Tools (⋮) option from the upper right corner.
- Select Extensions option from the drop-down menu to see extensions on your browser.
- Choose Exploit:JS/OVCExploit.gen related extensions then click on Uninstall button to remove it.
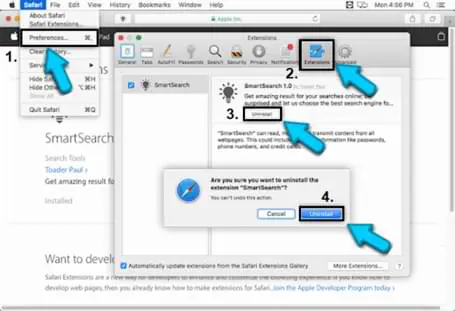
Remove Exploit:JS/OVCExploit.gen From Apple Safari
- Open Safari browser then tap on Preferences option from Safari menu.
- Open the Extensions tab, find Exploit:JS/OVCExploit.gen related extensions then click Uninstall button.
- Finally, again click the Uninstall button to remove the extension completely.
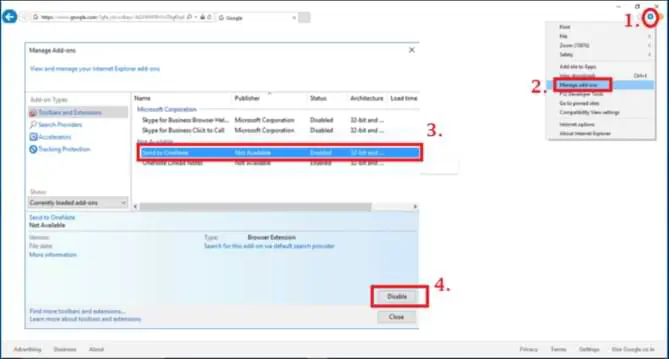
Remove Exploit:JS/OVCExploit.gen From Internet Explorer
- Open Internet Explorer then click on Menu option from the upper right corner.
- Select manage Add-ons option from drop-down list to see installed extension.
- Find Exploit:JS/OVCExploit.gen related extensions and click on Disable button to remove it.
Reset Browser Setting to Default
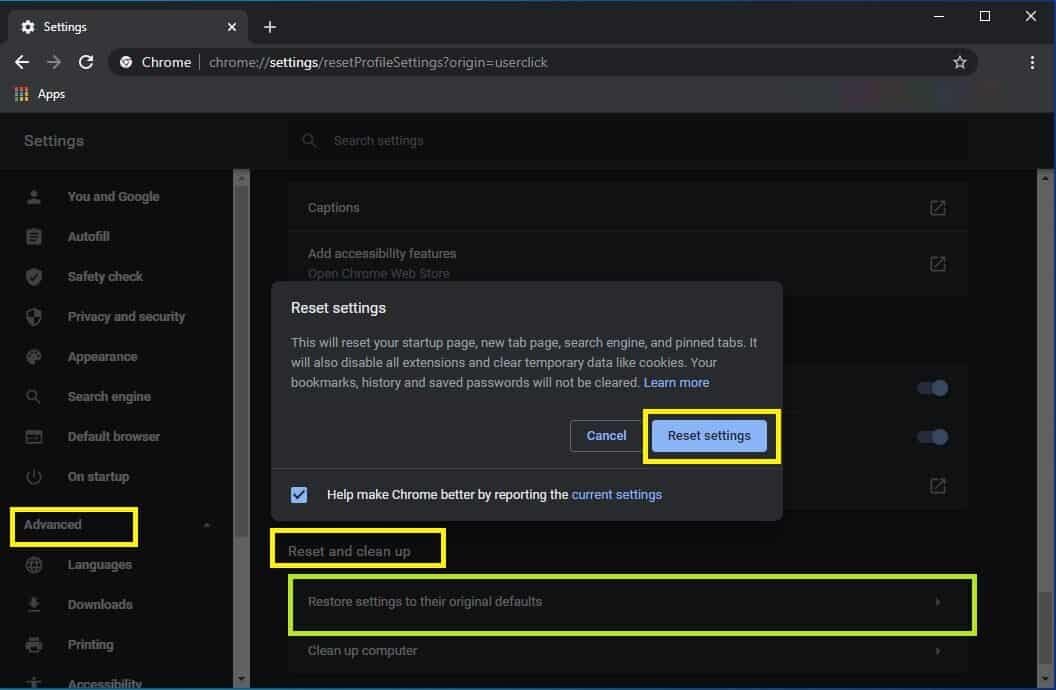
Once you remove Exploit:JS/OVCExploit.gen from your browser, you might want to reset the browser to default settings to reset any changes made by the virus. Follow below steps for that :Reset Google Chrome Web Browser
- Open Google Chrome, click on Menu (⋮) then select settings option.
- On Settings page, scroll down to the bottom, click Show Advanced settings option.
- From Reset and clean up click on Restore settings to their original defaults.
- Finally, click on Reset Settings button to reset your chrome browser.
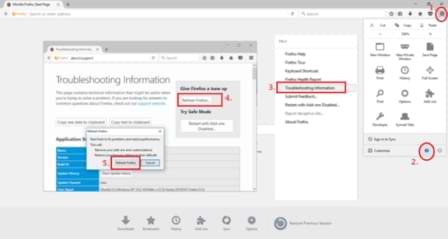
Reset Mozilla Firefox Browser
- Open Mozilla Firefox browser, click on Menu (☰) option, and select (?) icon.
- Click on Troubleshooting Information option from the drop-down menu.
- Then press the Refresh Firefox button and give confirmation.
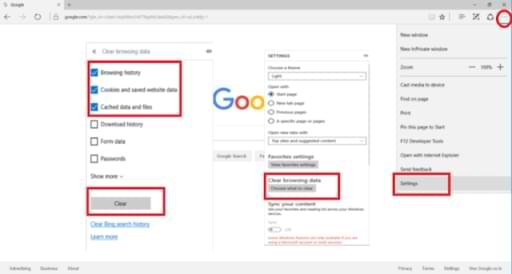
Reset MS Edge Browser
- Open MS Edge browser, click on More Tools (⋮) option, and select settings.
- Click on Choose what to clear Option, choose first three options then click on Clear button.
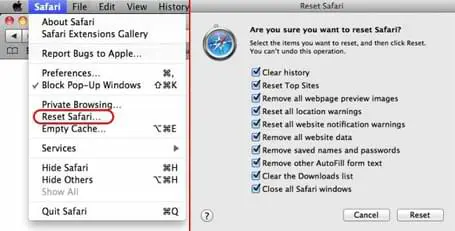
Reset Safari To Default
- Open Safari browser, tap on Safari menu, and select Reset Safari option.
- Now check all the boxes and then finally click on Reset button.
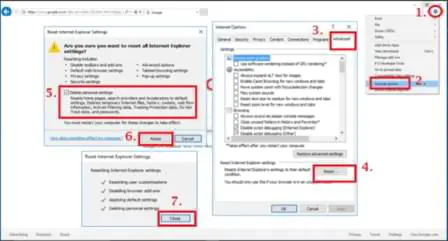
Reset Internet Explorer Browser
- Open Internet Explorer then click on Menu icon and hit Internet options.
- Visit Advanced tab, click Reset button, check Delete personal settings option, and hit Reset button.
How to Enable Browser Protection
Follow the below steps to enable built-in dangerous site protection in your web browsers. You can follow the same steps if you want to stop the malware protection on your browser.
Google Chrome – Dangerous Sites Protection
- Open your Chrome web browser, type “chrome://settings” in the URL bar, and press Enter.
- Got to bottom of the page and select “Show advanced settings” option.
- Look for the Privacy and security section then click on Sync and Google services.
- Now turn on the Safe Browsing (Protect you and your device from dangerous sites) option.
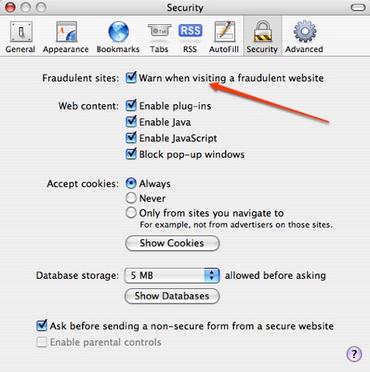
Safari Browser – Change Security preferences in Safari
- Open your Safari web browser, then tap on the Safari menu and select Preferences.
- Now you have to open the Security options on your Safari browser.
- Check Warn When Visiting a Fraudulent website box from the Fraudulent Sites section.
Mozilla Firefox – Block Attack Sites and Web Forgeries
- Open your Firefox web browser, click on Menu (☰) and select Options from the list.
- Now click on the Security option and then select the following items:
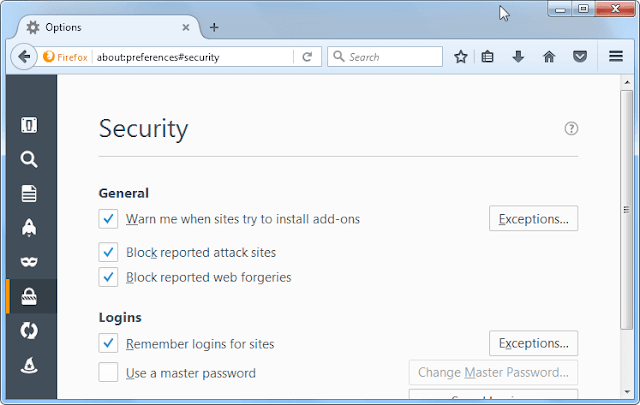
- Warn me when sites try to install add-ons
- Block reported attack sites
- Block reported web forgeries
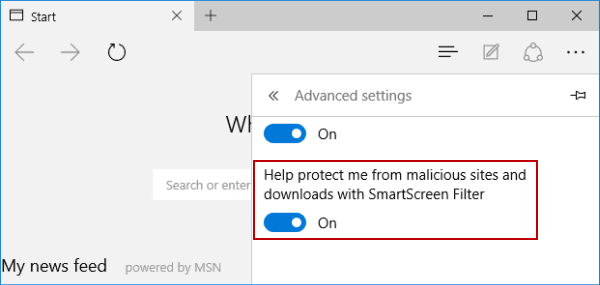
Edge Browser – Activate SmartScreen Filter
- Open your MS Edge web browser, click on More (⋮) icon from the upper right corner.
- Click on the Settings option from the Edge menu drop-down list.
- Scroll down and find View Advanced Settings option then open it.
- Turn ON the “help protect my PC from malicious sites and downloads with SmartScreen Filter” option.
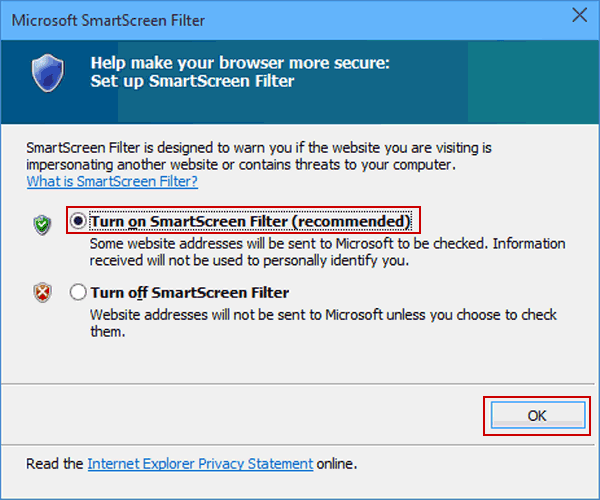
Internet Explorer – Activate Microsoft SmartScreen Filter
- Open your IE web browser, then click on Menu icon and hit Safety options.
- Now click on the SmartScreen Filter option from the drop-down list.
- Turn on SmartScreen Filter and restart your browser.
If you made these settings on your browser then phishing and malware protection on your browser is now active. But it does not mean that your computer cannot get infected by threats. These settings may block some dangerous and suspicious sites but there are other ways through which hackers can target your PC. So you must download a powerful Anti-Malware application on your computer that provides real-time protection to ensure your system security.
Tips To Prevent Exploit:JS/OVCExploit.gen Virus in Future
- Use a good anti-virus, be it a free version but don’t use cracked security programs.
- Make sure that your Windows firewall is active, so it can block upcoming threats.
- Keep your Windows OS and other programs updated to avoid vulnerabilities.
- Download updates only from official websites, don’t use suspicious sites.
- Never download and install pirated software, games, or illegal patches on your PC.
- Do not open spam emails from an unknown sender and scan all attachments before opening.
- Never download freeware third-party programs from unreliable sources or websites.
- Avoid connecting your PC to unsafe public Wi-Fi to protect your privacy.
- You can also use a VPN to spoof your connection and avoid malicious sites.
- Create a system restore point on your system for security purposes.
- Keep backup of all your important files to avoid data loss.
Some time threats like Exploit:JS/OVCExploit.gen keep getting back on the machine if all associated files are not removed. You are advised to use a Powerful Anti-Malware Tool to run a thorough scan of your PC and delete all threats at once.
Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)

Leave a Comment