Onelock is a dangerous ransomware that sneaks on the targeted machine without users’ permission. It is a data locking virus that is equipped with the latest encryption technology. It encrypts all the (documents, images, videos, audio, backup, database, etc.) and demands ransom for the decryption.
Encrypted files are marked with the “.onelock” extension. For example, a file named “myphoto.jpg” would appear as “myphoo.jpg.onelock” after encryption. Such renamed files are encoded and cannot be accessed without the decoder.
It is a MedusaLocker ransomware variant and generates ransom note “how_to_back_files.html” containing instructions to contact attackers and payment details to buy decryption tools. Read this guide to learn how to remove this virus and restore your files.
Threats like Onelock virus keep getting back on the PC if all associated files are not removed. So you are advised to use a powerful Malware Removal Tool to run a thorough scan of your PC and delete all threats at once.
Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)
What is Onelock?
Onelock is another nasty file-encrypting malware. This dubious threat is commonly known as the Onelock File Virus. If you see this infection on your system, then you are in big danger. This harmful virus will silently sneak into your machine and encrypt all your personal files. It will add its own extension to your filename as a prefix and leave a ransom note behind.

It is a sneaky malware infection. Once inside your computer, it will immediately corrupt all your files. It can disable your anti-virus and firewall security. You will not be able to remove this infection from your system. It will show a ransom message on your computer demanding money through cryptocurrency. It is a tricky situation because you can lose all your files due to this Onelock infection. So don’t make any decision in hurry.
Onelock is programmed to force victims to pay the ransom money and buy decryption software. However, there is no guarantee that you will recover all your files. Most of the ransomware victims get cheated and never get the decryption tools. Do not trust cyber criminals and never pay them money to buy access to your own files. This guide will help you to remove this threat and recover all your data.
How does your PC get infected?
There are several ways through which your system can get infected by a ransomware infection like this. They often get spread bundled with free third-party programs available for download on unreliable sites. Spam emails with malicious attachments could also drop this virus on your computer. It is very important to use custom installation and scan email attachments before opening.
Onelock Virus can also get distributed via other small threats that redirect your browser to suspicious sites which host malicious codes. Trojan horse and malware downloaders can also bring this infection to your PC. Browsing to porn or torrent sites and downloading cracked software or games could bring this virus to your system.
Onelock Ransomware: Threat Analysis
| Name | Onelock |
| Type | Ransomware, File-Encrypting virus |
| Extension | .Onelock |
| Threat Level | High (Encrypt all your data and Restrict access to your files). |
| Symptoms | Victims cannot access any files on their PC and find Ransom notes asking for money. |
| Damage | Onelock will encrypt your data by adding its extension to file names and demand ransom money for the decryption key |
| Distribution | It is mainly distributed through spam emails, bundled freeware, porn, or torrent sites. |
| Removal | Download SpyHunter 5 Anti-Malware |
| File Recovery | Download Data Recovery Software |
What to do after encryption?
As all your files are encrypted with military-grade encryption. Since you don’t have the decryption key, you need to get tricky. It is crucial that you do not contact cyber criminals. Remove your infected device from the network and create a backup copy of all the encrypted files on USB drives or cloud drives.
Paying ransom money to Onelock creators will do you no good. It is very much possible that attackers will stop communication after the payment. It is also possible that the decryptor won’t even work or bring more threats. So instead of paying the ransom, invest in a good security program.
Use powerful anti-malware software to completely remove Onelock virus from your PC. It will not recover your files but it will prevent further encryption of data. Later you can recover your encrypted files through Backup files. If you don’t have a backup then try any data recovery software.
Ransom note “how_to_back_files.html” contains the following instructions :
YOUR PERSONAL ID: - /!\ YOUR COMPANY NETWORK HAS BEEN PENETRATED /!\ All your important files have been encrypted! Your files are safe! Only modified. (RSA+AES) ANY ATTEMPT TO RESTORE YOUR FILES WITH THIRD-PARTY SOFTWARE WILL PERMANENTLY CORRUPT IT. DO NOT MODIFY ENCRYPTED FILES. DO NOT RENAME ENCRYPTED FILES. No software available on internet can help you. We are the only ones able to solve your problem. We gathered highly confidential/personal data. These data are currently stored on a private server. This server will be immediately destroyed after your payment. If you decide to not pay, we will release your data to public or re-seller. So you can expect your data to be publicly available in the near future.. We only seek money and our goal is not to damage your reputation or prevent your business from running. You will can send us 2-3 non-important files and we will decrypt it for free to prove we are able to give your files back. Contact us for price and get decryption software. qd7pcafncosqfqu3hr7tzwagzpcdcnytiw3b6varaeqv5yd.onion * Note that this server is available via Tor browser only Follow the instructions to open the link: 1. Type the addres "hxxps://www.torproject.org" in your Internet browser. It opens the Tor site. 2. Press "Download Tor", then press "Download Tor Browser Bundle", install and run it. 3. Now you have Tor browser. In the Tor Browser open qd7pcafncosqfqx4h6sr7tzwagzpcdcnytiw3b6varaeqv5yd.onion 4. Start a chat and follow the further instructions. If you can not use the above link, use the email: ithelp08@decorous.cyou ithelp08@wholeness.business * To contact us, create a new free email account on the site: protonmail.com IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.
How To Remove Onelock File Virus
Follow this guide carefully to remove this virus completely from your system. Below you can find step-by-step instructions on how to effectively get rid of this nasty threat easily. Removal of threats like Onelock Virus is never easy, so we have simplified the process for you in several small steps.
Quick Summary of Removal Instructions:
- Automatic Onelock Virus Removal Guide
- How To Decrypt .Onelock Files
- Manual Onelock Virus Removal Guide
- Start PC in Safe Mode With Networking
- Kill Malicious Process From Task Manager
- Remove Virus From Windows Registry Editor
- Remove Onelock Virus via system restore
- Prevent Onelock Virus in Future
Please Bookmark This Page by pressing the {ctrl+D} button or print it out on paper before you start the removal process because you may need to restart your PC or browser.
Automatic Onelock Virus Removal Guide
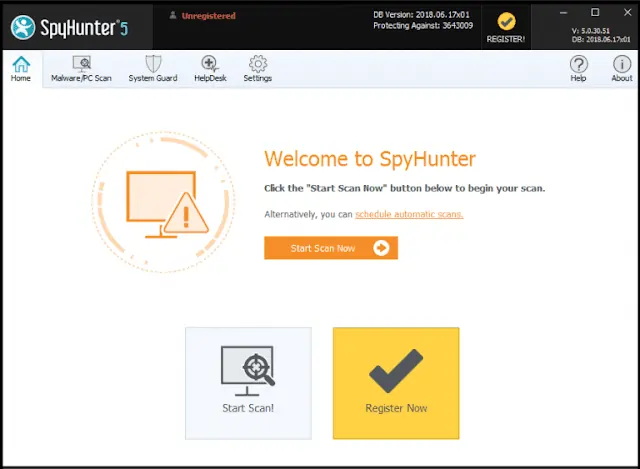
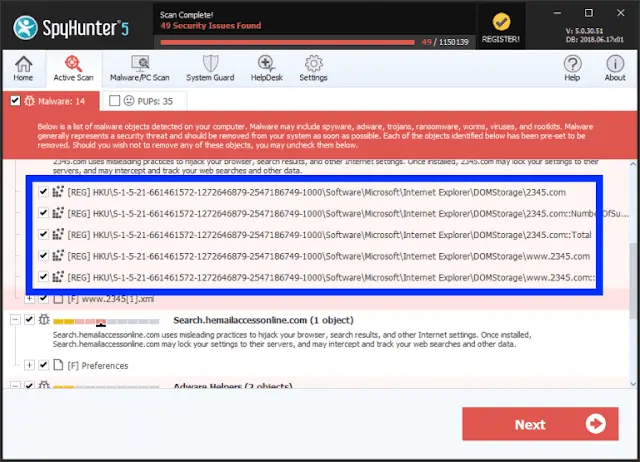
It can be hectic to remove threats from an infected PC but the use of powerful Anti-Malware can make it quite easy. SpyHunter anti-malware can help you to remove Trojan, Ransomware, Spyware, Adware, PUPs, etc. easily. You can scan your system for Onelock virus and all other hidden threats at once. All you need to do is to download this software and run a new scan on your PC.
It will find all the threats and viruses in no time and save you lots of time and effort. This amazing software also provides 24X7 customer support and one-on-one Spyware HelpDesk support for Custom Malware removal. Advanced System Guard feature detects and removes threats in real time. It has a very User-Friendly Interface and regular Malware definition updates make it most effective against the latest attacks.
How SpyHunter 5 Anti-Malware Works
- You will begin by downloading the software on your system for which you have to click on the below download button.
Geek’s Recommendation
Threats like Onelock Virus keep getting back on the machine if all associated files are not removed. So you are advised to use a powerful Malware Removal Tool to run a thorough scan of your PC and delete all threats at once.
Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)
- Once the software has been downloaded, double-click on SpyHunter-Installer.exe to install the Anti-Malware program on your PC and proceed with the setup.
- After installation, you will need to launch the Anti-Malware application. From the welcome screen click on the Start Scan Now button to initiate a new scan of your PC.
- Once the scanning process begins, it will take some time to run a thorough diagnostic of your PC and find all hidden threats and malware.
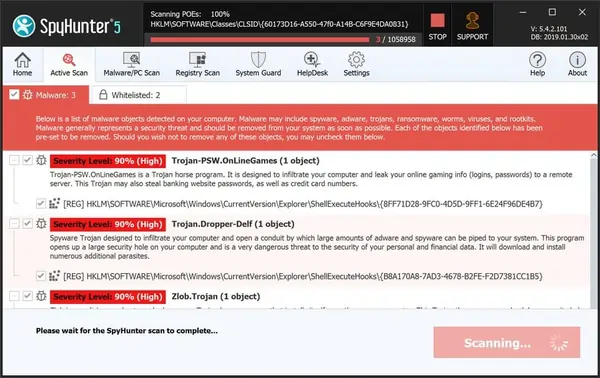
- Soon you will find a complete list of all the threats on your system screen. Then you will need to click on the Next button to delete all the viruses.
How To Decrypt .Onelock Files
As there is no Onelock ransomware decryptor available, you will need to use alternate options to restore your files. The first one is to use the backup. If you have created a backup of your important files then it is going to be quite easy. However, if you don’t have any backup files or they also got encrypted by the virus then you will have to try a data recovery software.
We recommend using Stellar Data Recovery software because it is a powerful and trusted data recovery software. Paying ransom money is not ideal because it will only motivate hackers to carry out more attacks. You can wait for any free decryptor to be launched but it can take forever. Download the free trial version of data recovery and scan your PC for files. It may be able to recover some of your files and save you lots of money.
- Click on the below download button to get started instantly with the data recovery process on your PC.
Download Data Recovery Software Now
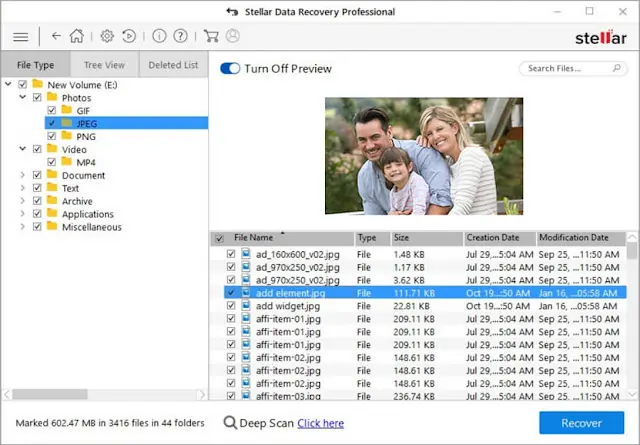
- After the download click on the installer file and complete the software installation. Then launch the application and select the Data type to recover, and click the Next button.
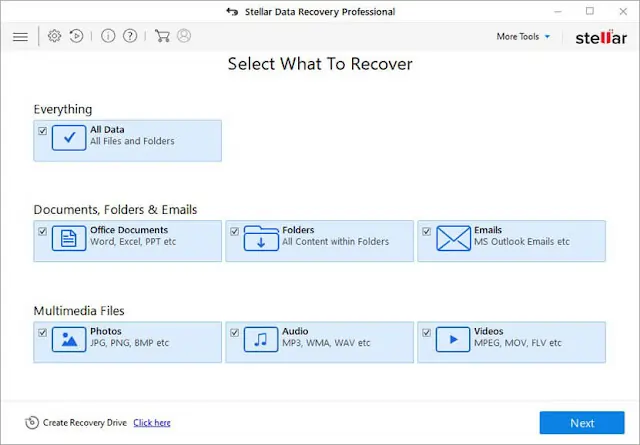
- After the selection of data, you will need to select the location from where you want to recover data. Choose the location and then click on the Scan button.

- The software will take some time to scan your system. You will see a list of all the files that can be recovered. You can preview them or click on the Recover button to save them.
Manual Onelock Virus Removal Guide
Attention! For the safety of your system, please confirm a few things before you begin manual removal:
- You have done this before, which means you have experience in removing the virus manually;
- That you know your way around PC and all necessary processes and applications;
- You know about Registry entry and the Serious repercussions of any mistake;
- Make sure you can reverse any mistake made during virus removal.
If you don’t attain any of the above standards, then manual removal could be a very risky idea. It is most likely best for you to use the SpyHunter 5 Anti-Malware which is totally secure and efficient method.
Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)
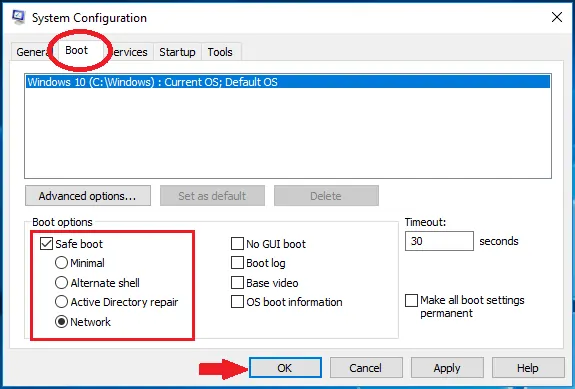
Start PC in safe mode with networking
- Click on the Windows and R keys together on your keyboard to open the Windows Run Box.
- Now you will need to type in MSConfig and then click the OK button.
- The System configuration settings box will appear on your computer screen.
- Click on the Boot tab, check the Safe Boot option, and select the network box,
- Finally, you will have to click on Apply and then press the OK button.
Kill Malicious Process From Task Manager
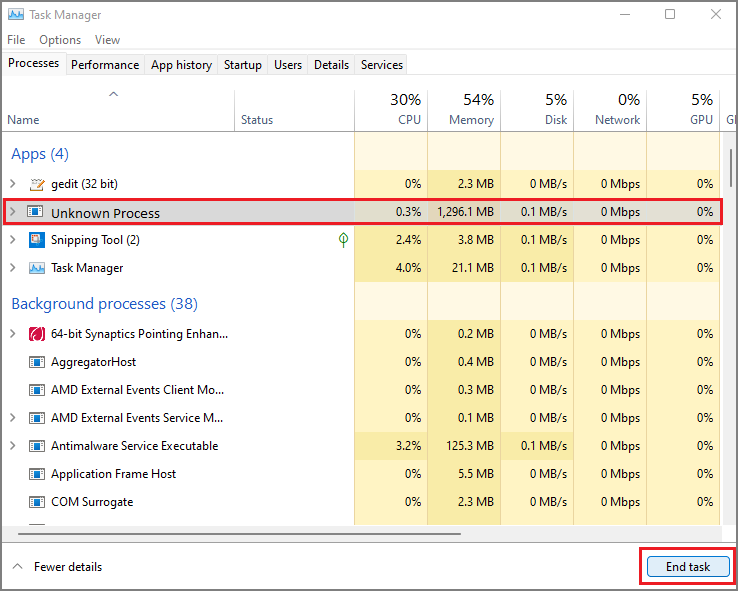
- Open the Windows Rub box again on your PC by pressing the Windows and R keys together on your keyboard.
- This time you will have to type in taskmgr and then click the OK button to open Windows Task Manager. Look for any unknown or malicious running on your system.
- Select the process which is taking lots of systems resources and then click on the End Task button.
Uninstall Onelock Virus from Control Panel
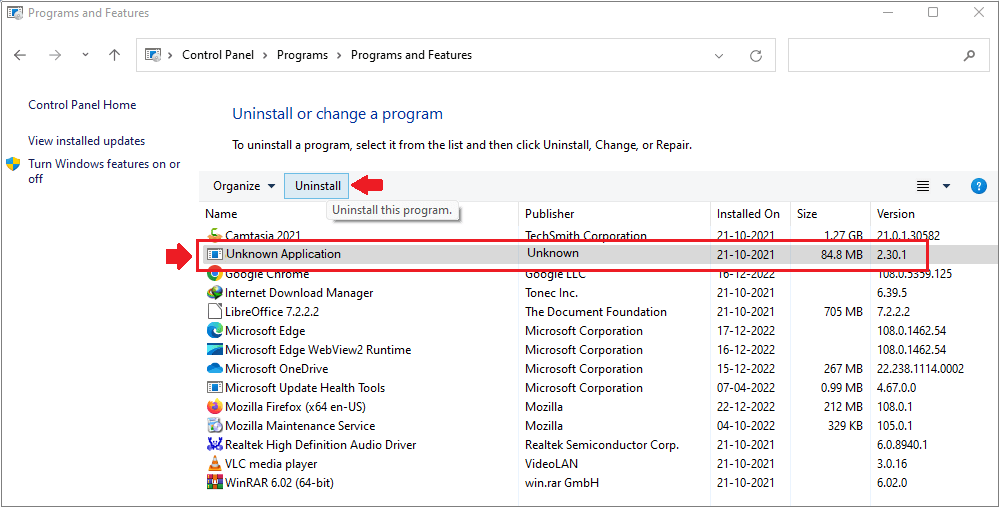
- Again you will need to open the Windows Run Box, so press the Windows and R keys together.
- This time you need to open the Windows Control Panel, so type in appwiz.cpl and then click the OK button.
- Programs and Features windows will appear on your computer screen with a list of all the installed applications.
- Now you need to look for any unknown or virus related program and then Uninstall it from your PC.
Remove Onelock Virus From Registry Editor
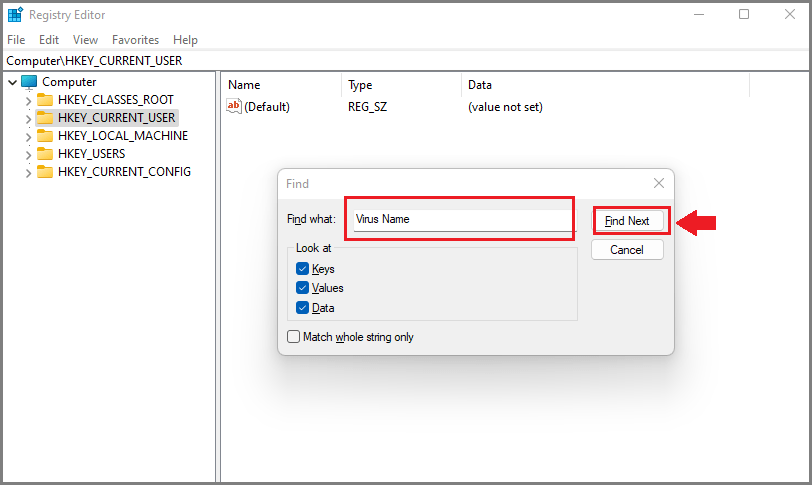
- Again open the Windows Run Box on your PC by using the Windows and R keys.
- To open the Windows Registry Editor, type in Regedit and click the OK button.
- Now you will have to find the virus related registry files and remove them.
- Press CTRL and F keys together on the keyboard to start a Find query.
- Type the virus name and click on Find Next button to find malicious entries and delete them.
Warning: Meddling with Windows Registry files might not be a good idea if you don’t have advanced knowledge about registry files. Deleting the wrong file can break down your entire system. Proceed at your own risk, or just skip this step. You can choose the Automatic Removal method and avoid all the problems.
Compatible with: Windows 11/10/8/7 (32 Bit and 64 Bit)
Remove Malicious IP addresses from Windows Hosts Files
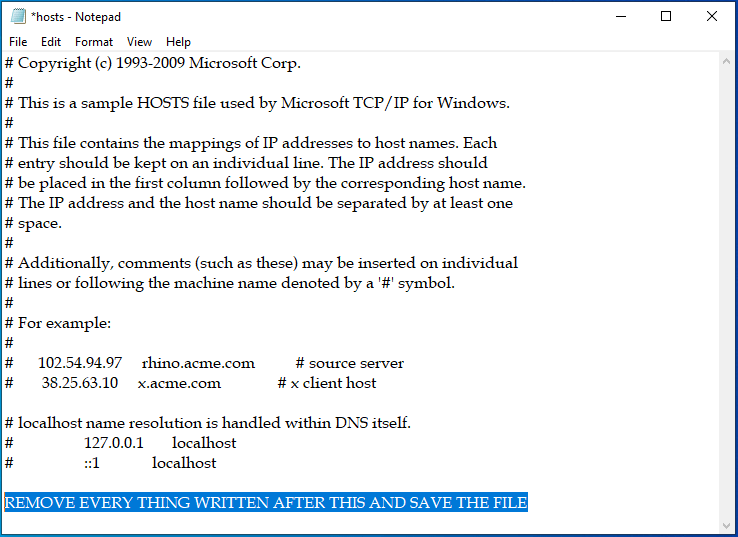
- To open the Windows hosts file, simply press the Windows and R keys together on the keyboard.
- Type C:\Windows\System32\drivers\etc in Run Box and then click the OK button.
- Now you will need to access the Windows hosts file using Notepad.
- Most threats add malicious IP addresses here to automatically connect to remote servers.
- Delete all the malicious IP addresses below the localhost and save the file.
Delete Virus related files from your PC
When malware infects your system, it normally creates several malicious files and spread them at different locations. After you remove the malware, these leftover files help them to get back to your computer. Remove all virus related files at once by following the below instruction :
- Open the Windows Run Box again by using the Windows and R keys together.
- Now you will open the below paths one by one using the Run Box and remove malicious files.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
For the first four options, look for any recent folder related to the Onelock File Virus and remove them. For the Temp folder, you can delete all the files at once. Use Ctrl, Shift, and Delete keys together for permanent removal.
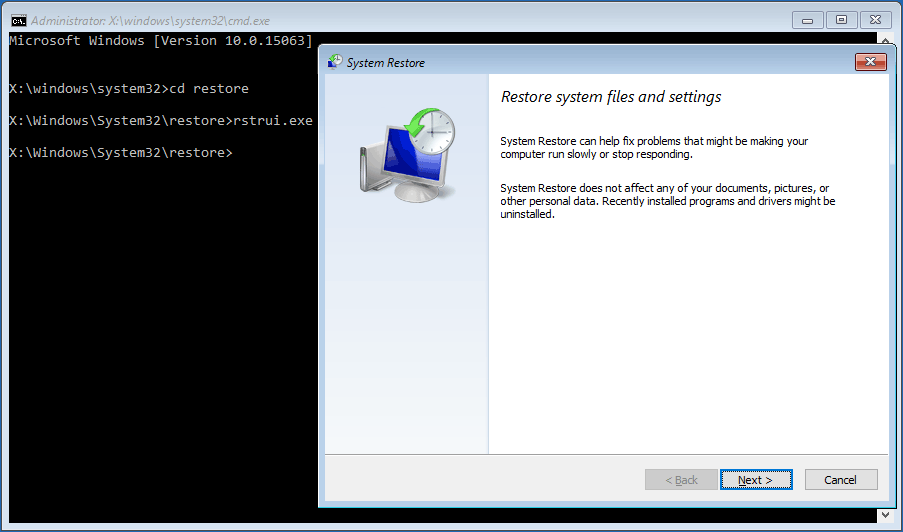
Remove Onelock Virus via system restore
- You will again need the Windows Run Box, so press the Windows and R keys together.
- Open the Command Prompt by typing in cmd and then clicking the OK button.
- Type cd restore and press Enter, then type rstrui.exe and press Enter.
- The System Restore window will get opened instantly then click on the Next button.
- Choose a System Restore point you have created in the past and click the Next button.
- Finally, when you will hit the Yes button, the system restoration process with start immediately.
Note: System restore to remove a virus will only work if you have a restore point set on your PC. Otherwise, no changes will be made to your system and it will not remove any threats. Be advised, restoring the computer to a previous version does not always guarantee virus removal. Most viruses delete restore points, so don’t get disappointed if this trick does not work for you.
Prevent Onelock Virus in Future
- Get a powerful Anti-Malware or Anti-virus to fight cyber threats. Free versions do not offer the best protection and cracked security programs can do more damage than good.
- Always keep your Windows firewall active, and your OS updated along with other important programs. Only download updates from official sites or reliable sources.
- Check HTTPS before entering your email, password, credit card details, etc. to any site. Do not visit sites that do not have SSL security. Also, don’t forget to Enable Phishing and Malware protection in Browser.
- Do not download or install any type of pirated software, games, or illegal patches. Avoid using shady sites to acquire freeware programs because they often use software bundling. Never install a program that asks you to inactivate your anti-virus software.
- Avoid opening spam emails from unknown senders. Always scan all the email attachments before opening them. Never click on any suspicious links with some too good to be true offers.
- Connecting your PC or mobile devices to unsafe public Wi-Fi is not a good idea. You can also avoid unwanted threats coming from malicious sites by using a VPN to spoof your connection.
- Keep regular backups of all your important data on external hard drives or cloud drives to avoid data loss in case of a ransomware attack. Also, create a system restore point on your system for security purposes.

Leave a Comment